Jon DiMaggio, Chief Security Strategist at threat intelligence platform Analyst1 released his findings about LockBit in a report called Ransomware Diaries: Volume 1. He said he used fake personas to communicate with members of the cybercriminal syndicate and learn more about their operations.
“LockBit is, right now, by far the worst among all the ransomware gangs,” DiMaggio told OCCRP. “They have by far the highest volume of attacks, and that’s a fact. They’re running the ransomware scene.”
He explained that until now, relatively little effort has been put into profiling the actors behind such cybercriminal syndicates. “I believe this is the first publicly-available, in-depth profile of any ransomware group,” he said.
“We need to get more people doing this, collecting data from the dark web, from these private channels, from the press releases on their websites. All this low-hanging fruit, it helps us better understand the adversary,” the expert said.
According to his report, LockBit’s leadership has been interacting with the wider cybercriminal community via dark web forums and private channels under the pseudonym LockBitSupp. This persona claims the group accesses its back-end infrastructure via Starlink, a U.S. satellite internet service owned by Musk’s SpaceX, and that they primarily rely on Bitcoin exchanges located in Hong Kong and China to launder proceeds from their ransomware campaigns.
The report also reveals LockBit’s close association with several other high-profile ransomware gangs. Though these relationships remain largely adversarial, due to the increasingly competitive nature of the global market for cybercriminal services, LockBit’s leadership appear to maintain a direct line of communication with multiple other criminal syndicates – including BlackCat, Hive, REvil, and DarkSide/BlackMatter, widely believed to have been responsible for the 2021 U.S. Colonial Pipeline cyberattack.
“Most of these relationships – not all, but most – started off well enough. But criminals have no ethics, so it’s usually just a matter of time before they step on each other’s toes and start pissing each other off,” DiMaggio said. “But at the end of the day, you’ve still got a lot of people who all know each other, who all run in the same circles, and who remain in communication with one another.”
LockBit also has ties to the ransomware group Blackbasta, formerly Conti, who were behind a series of large-scale cyber attacks that effectively paralyzed the Costa Rican government last year. According to LockBitSupp, DiMaggio says, Blackbasta are working for the Russian government, providing direct technical support to the FSB.
OCCRP previously reported how Moscow is likely to turn to cybercriminal proxies in launching future attacks against critical infrastructure in the West. In part because of the sheer scale and sophistication of Russia’s market for cybercriminal services, but also because of the “plausible deniability” afforded by such tactics.
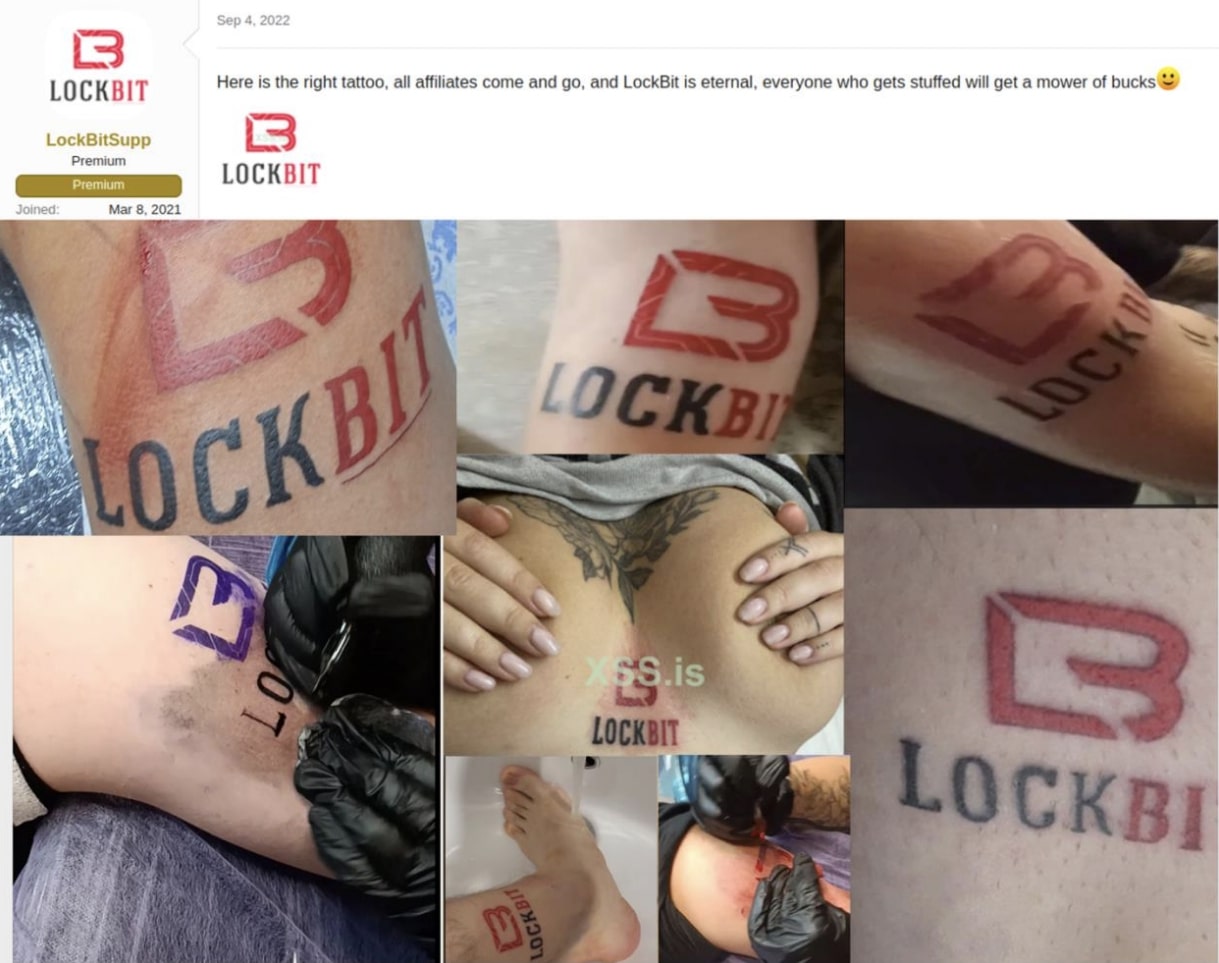
Beyond this, experts have also expressed alarm over the growing diversification of services and operational models within the cybercriminal community in recent years. The competition across this increasingly reputation-driven criminal sector is fierce, and has also created opportunities for accomplished hackers to effectively work as freelancers for multiple groups. It’s a trend keenly reflected by LockBit’s operations over the past few months, during which the group’s leadership has engaged in multiple smear campaigns against rival ransomware gangs, as well as launching several PR-stunts to promote their services and attract new blood.
The latter has included a “summer paper contest”, in which applicants were encouraged to submit academic-style papers on different hacking techniques, with the winner awarded a monetary prize. According to DiMaggio, this speaks to LockBit’s “outside-the-box” approach to raising awareness of their operations among prospective clients, as well as identifying and recruiting smart and upcoming cybercriminals, though their leaders’ showmanship has apparently attracted censure from other members of the cybercriminal community.
“At the end of the day, this is a very successful person, but who’s also very arrogant and insecure,” DiMaggio says. “They play a good chess game, but there’s a growing negative sentiment among other criminals who’re tired of the ego and constant chest pounding.”