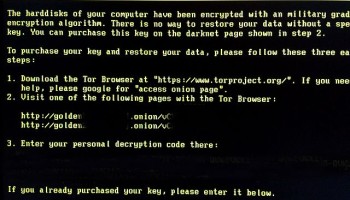
The malicious and fast-spreading "WannaCrypt" software blocks access to any files on a Microsoft PC, instead showing a message that demands a US$ 300 ransom to be paid into a Bitcoin wallet address, the Guardian reported.
"You only have three days to submit the payment," reads the message. "After that the price will be doubled. Also if you don’t pay in seven days, you won’t be able to recover your files forever."
The UK’s National Health Service (NHS) became the highest-profile victim. As a result, hospitals were forced to cancel operations and divert ambulances, while patient records and test results became inaccessible across England and Scotland.
Some of the largest companies in Spain and Portugal were also affected, including Telefónica. On Friday, the phone company ordered all 120,000 of its workers across 20 countries to turn off all equipment and disconnect from WiFi, according to Bio Bio Chile.
Similarly affected were FedEx, Germany’s Deutsche Bahn rail network, French Renault factories, China’s National Petroleum Corporation and Iranian universities, international media reported.
Within 48 hours, the cyberattack had hit 200,000 targets in at least 150 countries, Al Jazeera reported.
Although those behind the attack remain unknown, Bitcoin wallets are publicly visible. At the time of writing, 192 victims have paid a total of over 31.7 BTC (US$ 55,490) into three Bitcoin accounts.
The ransomware was temporarily brought to a halt Friday when an English cyber-security researcher accidentally activated a "kill switch" by purchasing a web domain for GBP £8 (US$ 10.34) that redirected the virus.
Experts believe, however, that the attackers will release newer variants of the malware unaffected by the kill switch.
Over the weekend, new cases were reported across Japan, South Korea and Taiwan, according to the New York Times.
Korean moviegoers Sunday at one cinema chain found themselves watching the ransom note instead of the programmed advertisements.
"We are in the face of an escalating threat," said Europol director Rob Wainwright, according to the Guardian. "I am worried about how the numbers will continue to grow when people go to work and turn [on] their machines on Monday morning."
In March, hacking group Shadow Brokers claimed to have stolen a code from a repository of NSA hacking tools. The code exploits a bug that allows worms to spread across networks, according to the Guardian.
Soon after the theft, Microsoft released a patch that fixed the vulnerability.
But those computers infected by the ransomware appear to be outdated devices that organizations deemed too expensive to upgrade, or too difficult to patch without disrupting crucial operations, the Guardian reported.
Nearly all NHS trusts were using an obsolete, 15-year-old version of Windows for which Microsoft had stopped providing security updates.
"The governments of the world should treat this attack as a wake-up call," said Microsoft’s president Brad Smith in a blog post. "An equivalent scenario with conventional weapons would be the U.S. military having some of its Tomahawk missiles stolen."
He called for governments to report vulnerabilities to tech vendors like Microsoft, rather than stockpile and exploit them.
The attack is so widespread that Intel has set up a page where visitors can follow the spread of malware in real time.